Staying safe online is more important than ever these days. With cyber threats on the rise, organizations and individuals alike need robust defenses to protect their sensitive information from hackers and malicious actors. That’s where a Security Operations Center (SOC) comes into play. Let’s delve into an overview of how a SOC keeps you safe online.
What Is a Security Operations Center?
A Security Operations Center (SOC) is a centralized unit that oversees and manages an organization’s cybersecurity. The main job of a SOC is to:
- Monitor the network and systems for any suspicious activity or potential attacks.
- Detect any security incidents or breaches as quickly as possible.
- Respond to those incidents by investigating, containing, and resolving the issue.
The SOC uses various tools and technologies, such as security information and event management (SIEM) systems, to gather data from across the organization. This creates a complete picture of the cybersecurity landscape and helps with effective responses to incidents.
Benefits of a Security Operations Center
Having a dedicated SOC team provides several key benefits for businesses and organizations:
- Improved Threat Detection: The SOC can quickly spot and respond to security threats before they cause major damage.
- Faster Incident Response: When a breach does occur, the SOC has the processes and expertise to contain it rapidly.
- Compliance and Risk Reduction: Meeting regulatory requirements and minimizing exposure to cyber risks is a core SOC responsibility.
- Proactive Defense: The SOC team analyzes threat intelligence to anticipate and prevent future attacks.
- Centralized Security Management: All cybersecurity operations are coordinated through the SOC for maximum visibility and control.
The SOC Team in Action
The Security Operations Center is made up of several key roles that work together:
- Security Analysts: Monitor systems, investigate alerts, and respond to incidents.
- Threat Hunters: Proactively search for hidden threats that evade detection.
- Incident Responders: Contain and mitigate the impact of security breaches.
- Security Engineers: Implement and maintain the SOC’s tools and technologies.
These experts use advanced security tools, threat intelligence, and human expertise to protect the organization.
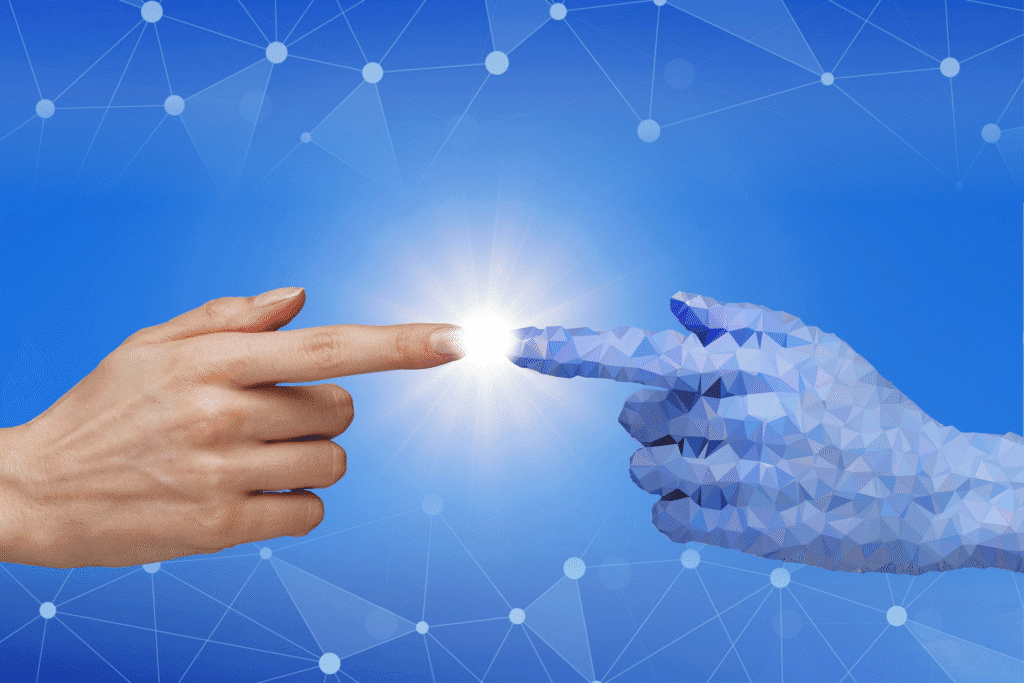
Choosing the Right SOC Model
There are a few different ways organizations can structure their Security Operations Center:
- In-House SOC: The SOC team is employed directly by the company and works onsite.
- Outsourced SOC: The SOC is run by a third-party cybersecurity provider.
- Hybrid SOC: A combination of in-house and outsourced security operations.
The right model depends on factors like the organization’s size, industry, budget, and security needs. Regardless of the approach, a well-designed SOC is crucial for safeguarding against modern cyber threats. With technology advancing every day and cyber threats shifting constantly, having a Security Operations Center is no longer a luxury but a necessity.